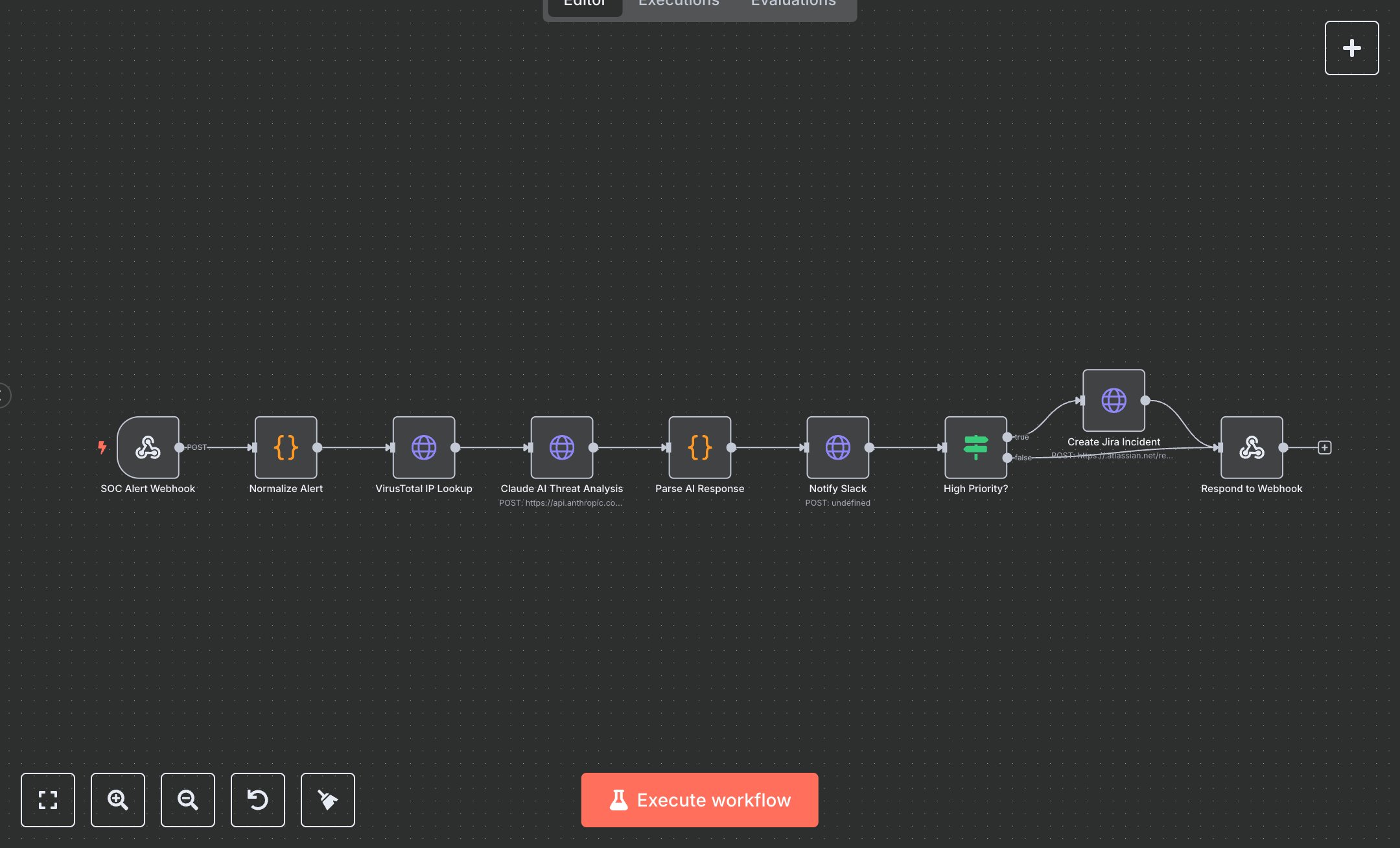
Claude AI SOC Analyst: Automated Threat Detection & Incident Response
This workflow deploys an AI-powered Security Operations Center analyst that automatically receives, normalizes, enriches, and triages security alerts from any SIEM platform — Splunk, Elastic, AWS GuardDuty, Wazuh, or Suricata. The moment an alert arrives via webhook, it is normalized into a standard format, the source IP is enriched with VirusTotal threat intelligence, and Claude claude-sonnet-4-6 performs a full threat assessment in seconds. What previously required a trained SOC analyst spending 20-45 minutes per alert is reduced to under 30 seconds per incident, with higher consistency and zero alert fatigue. The Claude AI analyst assigns a severity level (CRITICAL/HIGH/MEDIUM/LOW), maps the threat to a MITRE ATT&CK technique and tactic, generates a plain-English threat summary, lists 3-5 immediate response actions, scores false positive likelihood, and recommends escalation — all as structured JSON. Every alert triggers a rich Slack notification with color-coded severity. CRITICAL and HIGH alerts automatically create a Jira incident ticket with full context, affected asset details, and the response playbook pre-populated. Security teams handling 50-500 alerts per day save 15-30 analyst-hours weekly. ROI on a ,999 template pays back within the first week for any team paying k+ for SOC staff. Setup requires four credentials: an Anthropic API key (~$0.003 per alert analyzed), a VirusTotal API key (free tier: 500 lookups/day), a Slack incoming webhook URL (free), and Jira API credentials (optional — CRITICAL/HIGH path only). In n8n, add these as workflow variables: ANTHROPIC_API_KEY, VIRUSTOTAL_API_KEY, SLACK_WEBHOOK_URL, JIRA_DOMAIN, JIRA_EMAIL, JIRA_API_TOKEN, JIRA_PROJECT_KEY. Activate the workflow, copy the webhook URL from the SOC Alert Webhook node, and configure your SIEM to POST alerts to that endpoint. Test by sending a sample JSON payload with fields: src_ip, type, severity, hostname. Common errors: 401 on VirusTotal means invalid API key; 403 on Jira means token lacks Create Issue permission; Claude returning non-JSON means the alert description contained formatting that confused the parser — the Code node handles this gracefully with a fallback. Monitor execution logs weekly and review Claude's severity assessments against your team's judgement for the first two weeks to calibrate confidence.
$5.49
Workflow steps: 9
Integrated apps: webhook, code, httpRequest